Biometric Onboarding Surge Gold_ Revolutionizing Digital Access in the Modern Era
Welcome to the forefront of digital security, where cutting-edge technology meets user convenience in a seamless, secure experience. This is "Biometric Onboarding Surge Gold," a groundbreaking approach that’s redefining how we access and verify identities in the digital world.
The Evolution of Digital Security
In an era where data breaches and identity theft are rampant, traditional password and PIN systems are becoming increasingly obsolete. Biometric Onboarding Surge Gold emerges as a beacon of innovation, offering a robust, secure, and user-friendly alternative. This method utilizes unique biological traits like fingerprints, facial recognition, and even iris scans to verify identity, ensuring that only authorized individuals gain access.
What Sets Surge Gold Apart?
The name "Surge Gold" isn’t just a catchy moniker; it signifies the pinnacle of biometric technology. Here’s what makes it stand out:
Unmatched Security: Unlike passwords, biometric traits are immutable. Once set, they cannot be stolen or guessed. This drastically reduces the risk of unauthorized access.
Seamless User Experience: Forget the frustration of remembering complex passwords or dealing with forgotten PINs. With Surge Gold, users simply need to scan their fingerprint or face to unlock access, making the process incredibly straightforward.
Advanced Technology: Surge Gold employs the latest in biometric verification technologies, including multi-factor authentication. This means that even if one biometric trait is compromised, additional layers of security still protect the user.
The Technology Behind the Magic
To appreciate the brilliance of Surge Gold, let's take a closer look at the technology underpinning it.
1. Multi-Modal Biometrics
Surge Gold doesn’t rely on a single biometric trait but instead integrates multiple modalities. This means that even if one biometric type is compromised, others can still provide a secure verification process. For instance, if your fingerprint is stolen, facial recognition and iris scans will still keep you safe.
2. Artificial Intelligence and Machine Learning
At the core of Surge Gold lies advanced AI and machine learning. These technologies analyze biometric data in real-time, identifying patterns and anomalies. This ensures that even subtle changes in a user’s biometric traits—such as a change in facial expression or a slight shift in iris pattern—trigger additional verification checks, enhancing security.
3. Cryptographic Security
Surge Gold employs state-of-the-art cryptographic techniques to secure biometric data. Unlike passwords, which can be hacked and reused, biometric data is encrypted and stored in a way that even if it’s intercepted, it cannot be replicated or misused.
Transforming Industries
The benefits of Surge Gold extend far beyond personal digital security. Several industries are leveraging this technology to revolutionize their security protocols.
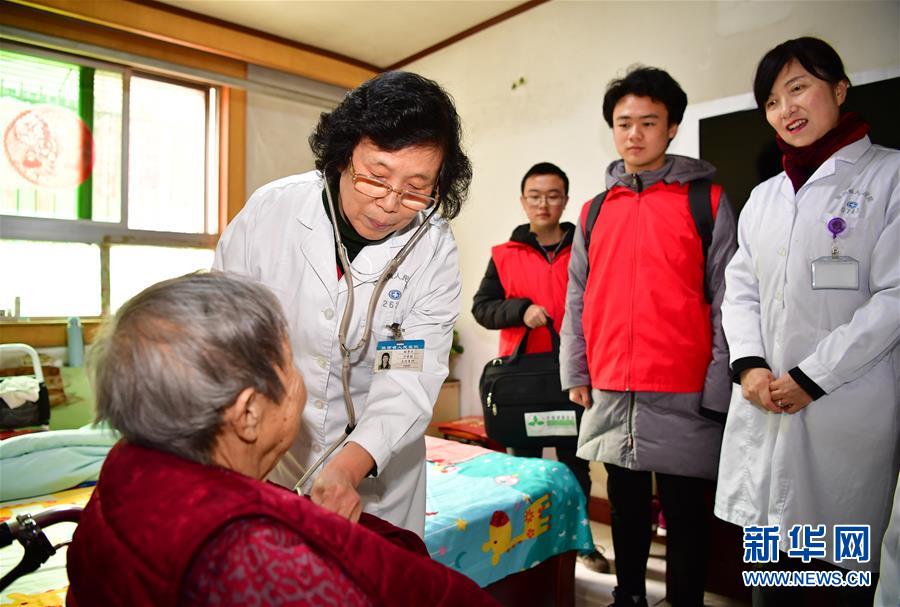
Healthcare
In healthcare, where patient privacy is paramount, Surge Gold ensures that only authorized personnel can access sensitive patient information. This not only enhances security but also streamlines administrative processes, allowing healthcare providers to focus more on patient care.
Financial Services
The financial sector, notorious for being a prime target for cyber-attacks, benefits immensely from Surge Gold. Banks and financial institutions use it to secure transactions and protect against fraud, offering customers a peace of mind knowing their financial information is in safe hands.
Corporate Security
Corporations use Surge Gold to secure access to sensitive corporate data. This is particularly crucial in industries like defense, aerospace, and pharmaceuticals, where the stakes are incredibly high.
The Future of Biometric Onboarding
As we look to the future, Surge Gold is just the beginning. The ongoing advancements in biometric technology promise even more sophisticated and user-friendly solutions. From voice recognition to behavioral biometrics, the horizon of digital security is bright and full of promise.
Conclusion
Biometric Onboarding Surge Gold represents a significant leap forward in digital security. By combining unmatched security with seamless user experience, it’s not just a technology but a revolution. As we continue to navigate the digital landscape, Surge Gold will undoubtedly play a crucial role in shaping a safer, more secure future.
Stay tuned for part two, where we’ll delve deeper into real-world applications and how Surge Gold is making a tangible difference in various sectors.
Welcome back to our exploration of Biometric Onboarding Surge Gold. In this second part, we’ll dive deeper into real-world applications and how this transformative technology is making a tangible difference across various sectors.
Real-World Applications
1. Government and Public Safety
Governments worldwide are adopting Surge Gold to enhance public safety and streamline service delivery. From secure access to government databases to biometric voter registration, this technology plays a crucial role in ensuring transparency and security.
2. Retail and E-commerce
In the retail sector, Surge Gold is revolutionizing the customer experience. Retailers are using it to secure access to employee accounts and protect against theft. In e-commerce, it’s being used to verify the identity of users during transactions, ensuring secure and seamless online shopping experiences.
3. Education
Educational institutions are leveraging Surge Gold to secure access to sensitive student data and administrative systems. This not only protects student privacy but also ensures that only authorized personnel can access critical information.
Making a Tangible Difference
Enhanced Security
One of the most significant impacts of Surge Gold is the enhanced security it provides. By eliminating the reliance on passwords and PINs, it drastically reduces the risk of data breaches and identity theft. This is particularly crucial in sectors like healthcare and finance, where data security is paramount.
Streamlined Processes
Surge Gold is also streamlining processes across various industries. For instance, in corporate environments, it’s simplifying access control, reducing the administrative burden on security teams, and ensuring that only authorized personnel have access to sensitive areas and data.
Improved User Experience
The user experience has also seen a remarkable improvement with Surge Gold. No longer do users have to remember complex passwords or deal with the frustration of forgotten PINs. The seamless, intuitive nature of biometric verification means users can access their accounts quickly and easily, enhancing satisfaction and productivity.
Case Studies
Healthcare: Protecting Patient Privacy
In a leading hospital, Surge Gold has been implemented to secure access to patient records. This has not only enhanced security but also reduced the administrative burden on staff. With biometric verification, doctors and nurses can quickly access patient information, leading to better, more efficient care.
Finance: Ensuring Secure Transactions
A major bank has adopted Surge Gold to secure online banking transactions. This has significantly reduced instances of fraud and unauthorized access, giving customers peace of mind when managing their finances online.
Corporate: Streamlining Access Control
A multinational corporation uses Surge Gold to manage access to its corporate network. This has simplified the access control process, ensuring that only authorized personnel can access sensitive data and areas, thereby enhancing overall security.
The Road Ahead
Innovations on the Horizon
The future of biometric technology looks incredibly promising. Innovations like liveness detection—which verifies that the biometric trait being scanned is live and not a photo or fake—are on the horizon. This will further enhance the security of biometric systems.
Expanding Applications
As we continue to innovate, we can expect Surge Gold to find applications in even more sectors. From smart homes to autonomous vehicles, the potential uses of biometric onboarding are vast and varied.
Conclusion
Biometric Onboarding Surge Gold is more than just a technological advancement; it’s a revolution in the way we think about digital security. By offering unparalleled security, streamlining processes, and enhancing the user experience, it’s making a tangible difference across various sectors. As we look to the future, the potential of Surge Gold is limitless, promising a safer, more secure digital world.
Thank you for joining us on this journey through the innovative world of biometric onboarding. Stay tuned for more insights into how technology is transforming our lives.
I hope this detailed exploration of "Biometric Onboarding Surge Gold" captivates your interest and provides a comprehensive understanding of its impact and potential. If you have any specific questions or need further details, feel free to ask!
Identifying Risky Projects for Strategic Investment
In the ever-evolving world of strategic investment, discerning which projects carry the highest risk is not just a matter of caution—it’s an art form. As investors, our goal is to balance the potential for significant returns with the necessity of mitigating risk. This requires a keen eye for detail, a robust analytical framework, and a willingness to delve into the complexities that often accompany high-stakes ventures.
The Anatomy of Risk:
Understanding what makes a project risky begins with identifying the various types of risk involved. Financial risk, operational risk, market risk, and strategic risk are all potential areas where a project could falter. Financial risk involves the potential for losses in the project’s funding or revenue streams. Operational risk relates to internal processes, such as supply chain disruptions or technology failures. Market risk encompasses external factors like changing consumer preferences or shifts in competitive dynamics. Lastly, strategic risk involves the alignment of the project with the overall business strategy.
Metrics to Watch:
To effectively identify risky projects, one must look beyond simple surface-level indicators. While metrics like Return on Investment (ROI) and net present value (NPV) provide a foundational understanding, deeper analysis is required. Here are some key metrics to consider:
Projected Revenue vs. Historical Data: Compare the projected revenue of a new project with the historical performance of similar ventures. Significant deviations may indicate potential issues.
Debt-to-Equity Ratio: A high debt-to-equity ratio can signify that a project is heavily leveraged, which increases financial risk.
Burn Rate: For startups and early-stage projects, the burn rate—how quickly the company is spending its capital—can be a critical indicator of long-term viability.
Market Penetration Rate: How quickly a project is gaining market share can offer insights into its competitive advantage and potential for growth.
Frameworks for Analysis:
Several frameworks can aid in the evaluation of project risk:
SWOT Analysis: This classic tool assesses Strengths, Weaknesses, Opportunities, and Threats, providing a comprehensive overview of a project’s potential and challenges.
PESTLE Analysis: Examining Political, Economic, Social, Technological, Legal, and Environmental factors helps in understanding the external environment in which a project operates.
Scenario Analysis: By developing multiple potential future scenarios, investors can better understand the range of outcomes and their associated risks.
Monte Carlo Simulation: This statistical technique uses random sampling and mathematical modeling to predict the probability of different outcomes, offering a probabilistic approach to risk assessment.
Red Flags in Project Evaluation:
Certain red flags should trigger a closer examination:
Inconsistent or Vague Financial Projections: If the financial forecasts lack detail or seem overly optimistic without a clear rationale, it may be a sign of trouble ahead.
Lack of Experienced Leadership: Projects led by inexperienced or unproven management teams often carry higher risks.
Over-reliance on a Single Revenue Stream: Projects that depend heavily on one source of income are inherently riskier than those with diversified revenue streams.
Final Thoughts:
Identifying risky projects for strategic investment involves a meticulous blend of analytical rigor and intuition. By understanding the different types of risk, employing robust metrics, utilizing analytical frameworks, and being vigilant for red flags, investors can better navigate the complex terrain of high-stakes ventures. The next part of this article will delve deeper into case studies and real-world examples to illustrate these principles in action.
Identifying Risky Projects for Strategic Investment: Real-World Insights
Building on the foundational understanding of risk types, metrics, and analytical frameworks, this second part of our exploration will delve into real-world examples and case studies. These practical illustrations will offer a clearer picture of how theoretical principles can be applied to identify risky projects and make informed strategic investment decisions.
Case Studies: Learning from the Past
History is replete with examples of both successful and failed investments, each offering valuable lessons. Let’s explore a few notable case studies to understand how risky projects were identified and the outcomes that followed.
1. The Rise and Fall of Blockbuster:
Blockbuster was once the quintessential video rental store, dominating the market with its vast network of physical stores. However, its failure to adapt to the digital revolution highlights the importance of market risk analysis. While the company was heavily invested in its brick-and-mortar model, digital streaming services like Netflix began to gain traction. Blockbuster’s reluctance to embrace this technological shift, coupled with its high operational costs, eventually led to its downfall. This case underscores the necessity of staying attuned to market trends and technological advancements.
2. Theranos: A Cautionary Tale of Over-Optimism:
Theranos, a healthcare company founded by Elizabeth Holmes, promised revolutionary blood testing technology. Initial projections and enthusiasm were sky-high, but underlying issues soon came to light. The company’s technology was found to be ineffective, and its business model unsustainable. This case highlights the dangers of overly optimistic financial projections and the importance of rigorous due diligence.
3. Nokia’s Missed Opportunity with Smartphones:
Nokia was a dominant player in the mobile phone market during the early 2000s. However, the company’s failure to adapt to the smartphone revolution led to a significant loss of market share to competitors like Apple and Samsung. This case illustrates the risks of not aligning strategic initiatives with market trends and technological advancements.
Applying Frameworks in Real-World Contexts:
Let’s explore how the analytical frameworks discussed in part one can be applied to real-world scenarios.
1. Using SWOT Analysis for Project Evaluation:
Consider a tech startup developing a new social media platform. A SWOT analysis might reveal:
Strengths: A unique user interface, a strong team of developers, and initial user engagement. Weaknesses: Limited marketing budget, lack of brand recognition. Opportunities: Growing trend in social networking, potential for partnerships. Threats: Established competitors, rapidly evolving technology.
This analysis can help investors understand both the potential and the challenges of the project.
2. Scenario Planning in Practice:
Imagine an investor evaluating a renewable energy project. By developing multiple scenarios—such as favorable government subsidies, neutral market conditions, and adverse regulatory changes—the investor can better understand the range of possible outcomes and prepare for contingencies.
3. Monte Carlo Simulation in Action:
A financial institution might use Monte Carlo simulation to assess the risk of a new investment portfolio. By running thousands of simulations, the institution can estimate the probability of different outcomes, helping to identify the most likely scenarios and associated risks.
Risk Mitigation Strategies:
Identifying risky projects is just the first step. The next crucial phase is developing strategies to mitigate these risks. Here are some approaches:
Diversification: Spreading investments across multiple projects or sectors can reduce the impact of any single risky venture.
Hedging: Utilizing financial instruments like options and futures to protect against adverse market movements.
Staged Investment: Investing in phases, allowing for reassessment and exit strategies if early indicators point to high risk.
Due Diligence: Conducting thorough background checks, financial audits, and management assessments before committing significant resources.
Final Thoughts:
In the dynamic landscape of strategic investment, identifying risky projects is an ongoing process that requires a blend of analytical skill, intuition, and practical experience. By examining real-world case studies and applying robust analytical frameworks, investors can make more informed decisions. The next step is to continually refine these strategies and adapt to the ever-changing market conditions.
Understanding the art and science of identifying risky projects is essential for safeguarding investments and maximizing returns. This comprehensive approach not only helps in recognizing potential pitfalls but also empowers investors to seize opportunities with confidence and caution.
In conclusion, the journey to mastering strategic investment is one of continuous learning and adaptation. By staying informed, vigilant, and open to new insights, investors can navigate the complexities of high-stakes ventures and achieve their financial goals.
Exploring the Future_ Web3 Community Incentive Models
Top Earn Passive Income in Cross-Chain Interoperability 2026 with Low Risk_2